Your go-to tech lighthouse nestled in the scenic heart of Atlantic Canada. As maritimers, we're not just known for our friendliness, but also for our expertise in tailoring a wide range of IT services for small businesses. We offer everything from web development to upkeep, ensuring your ship sails smoothly in the digital sea. Guided by the lighthouse beam of SEO and social media, we amplify your online visibility, helping your venture reach new horizons. Our expert crew provides seasoned consulting, ensuring your digital navigation is always on the right course. If you're looking to open up shop in the bustling market of eCommerce, we've got you covered with user-friendly online stores that reflect your unique brand. Here at Lets Nurture, we’re true to our maritimer spirit, aiding growth, and harnessing the power of technology to brave the changing tides of business. Hop aboard and set sail towards digital prosperity with us!
- Tech Services

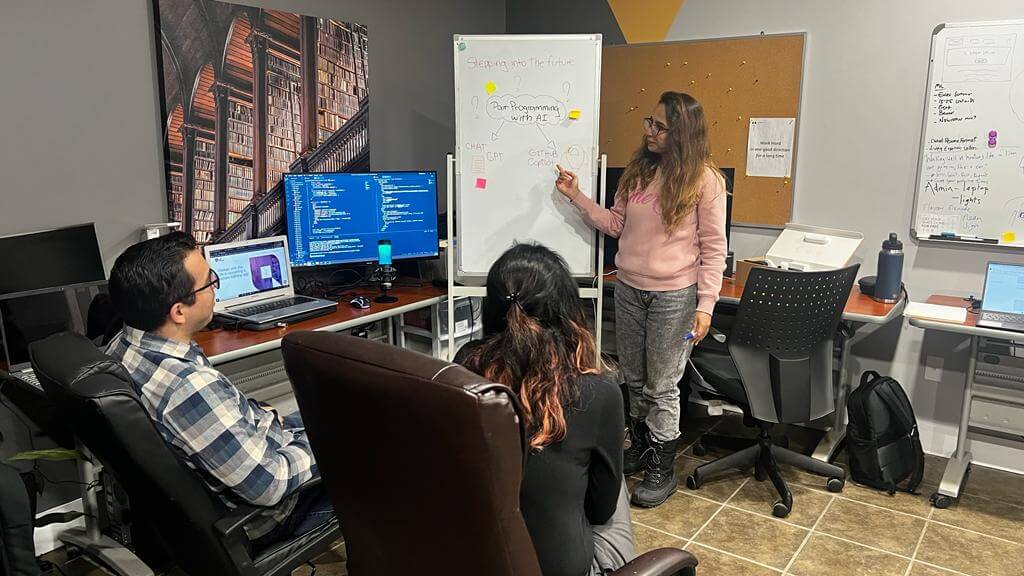
Concept Development
- Industry
- Emerging Tech
- Blog
- Contact Us